The Ultimate Guide to Privileged Access Management
A curated Irish edition of TechDay news, analysis, interviews, reviews, job moves, and related resources for Privileged Access Management (PAM).
What to know about Privileged Access Management
Privileged Access Management (PAM) is a critical component of cybersecurity focused on securing, controlling, and monitoring privileged accounts and access within an organisation. Privileged access refers to elevated permissions that allow users to perform sensitive operations in IT systems, networks, cloud environments, and applications. Managing these privileges effectively helps prevent insider threats, credential theft, and external cyberattacks that can lead to severe data breaches or operational disruptions.
The stories tagged with Privileged Access Management highlight industry developments such as new product features, security enhancements, integrations with cloud services, AI-powered automation, and partnerships aiming to strengthen PAM strategies. They emphasize challenges organisations face in maintaining visibility and control over privileged accounts, especially as hybrid cloud architectures, DevOps workflows, and remote work increase the complexity of access management.
Reading about Privileged Access Management on our blog provides insights into best practices for implementing least privilege principles, just-in-time access, multi-factor authentication, and zero trust security models. The content also underscores regulatory compliance considerations and the evolving threat landscape, including ransomware and insider misuse. By exploring these stories, readers can learn how PAM solutions adapt to emerging technologies and cyber risks to safeguard critical infrastructure and sensitive information effectively.
Analyst Insights
Research and market analysis connected to Privileged Access ManagementFeatured News

How Formula 1 turns data & cyber security into speed
At Albert Park, F1 insiders reveal how sharper data use, tighter security and resilience planning combine to unlock race-winning performance.

Consolidation Wave Hits Infosec, Sparing CISOs From Tool Sprawl
Overwhelmed CISOs are driving a consolidation wave in cybersecurity, slashing tool sprawl to close security gaps and cut mounting costs.
Expert Columns
Interviews
Interviews and video coverage from the networkRecent Privileged Access Management News

Genetec urges tighter identity controls for security systems
Genetec warns AI-driven attacks are exposing weak passwords and access gaps in connected cameras, doors and cloud-based security systems.
Recast adds Intune tools for hybrid endpoint teams
Recast expands Right Click Tools with Intune, Autopilot and patching updates to help hybrid Microsoft endpoint teams manage devices from one place.

Keeper Security launches Agent Kit for AI coding agents
Keeper Security launches Agent Kit to let AI coding assistants handle secrets and admin tasks without exposing credentials in chat logs.
.webp)
Qualys warns cloud risk now stems from identity design
Qualys report says cloud breaches are increasingly driven by identity design, delegated trust and slow remediation as AI widens exposure.

Critical Microsoft vulnerabilities double in yearly report
Critical Microsoft flaws double as Azure and Dynamics 365 risks surge, BeyondTrust warns organisations to prioritise identity and privilege controls.

Sysdig report says cloud security shifts to machine speed
Sysdig says companies are increasingly leaning on automated defence as AI-driven attacks accelerate, with machine identities now dominating cloud access.

Keeper boosts endpoint privilege governance for firms
Keeper Security adds approval workflows and audit logging to Endpoint Privilege Manager as enterprises tighten control over temporary admin access.
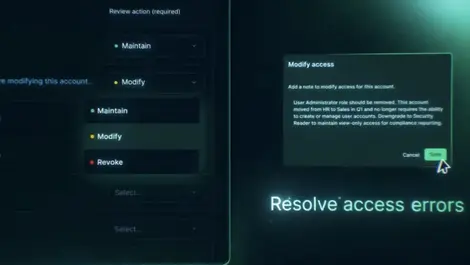
Secureframe launches access review tool for compliance teams
Secureframe adds user access reviews to Comply platform to help compliance teams replace spreadsheets and email with a single audit-ready workflow.

Attackers exploit trust in Blackpoint Cyber report
Blackpoint Cyber warns attackers are increasingly slipping in through trusted credentials, VPNs and remote tools, with fake CAPTCHA scams leading incidents.

Exabeam expands AI agent analytics to ChatGPT, Copilot
Exabeam widens AI agent monitoring to ChatGPT and Copilot, as chief AI and product officer Steve Wilson says digital workers need closer oversight.

Bitdefender launches free attack surface assessment
Bitdefender offers free 45-day internal security check to spot over-entitled staff access as attackers increasingly abuse trusted tools.

RSA expands Microsoft tie-up with passwordless access
RSA deepens its Microsoft 365 E7 alliance to secure human and AI identities, rolling out wider passwordless access across complex estates.

AI agents blur human access lines in enterprise systems
Most organisations cannot distinguish AI agents from human staff, exposing widening identity and access risks as autonomous tools spread.

BeyondTrust warns of 467% rise in enterprise AI agents
BeyondTrust warns a surge of unsupervised AI agents is creating a hidden “shadow workforce” with admin-level access inside enterprises.

Saviynt launches AI agent identity security platform
Saviynt unveils an AI identity security platform to govern autonomous agents across major enterprise AI stacks and close emerging access gaps.

Sysdig launches runtime security for AI coding agents
Sysdig unveils runtime security for AI coding agents, promising real-time monitoring of autonomous dev tools to curb emerging risks.

BeyondTrust expands Pathfinder to secure AI agents
BeyondTrust expands Pathfinder to discover, govern and lock down proliferating enterprise AI agents, identities, privileges and secrets.

Rubrik deepens identity security & AI governance push
Rubrik links Microsoft Defender with new AI governance engine SAGE to speed identity attack recovery and tighten control of autonomous agents.

Yubico & Delinea link AI actions to human approval
Yubico and Delinea unite hardware keys with identity checks to ensure each high‑risk AI agent action is explicitly approved by a human.

Netwrix boosts AI data governance for Microsoft Copilot
Netwrix enhances its 1Secure platform to map AI access, tightening data governance and Copilot monitoring across hybrid environments.



